
หลังจากคราวที่แล้วได้เล่าถึงความสามารถในการ Monitor ผู้ใช้งานและอุปกรณ์ในระบบเครือข่ายในเชิงลึกของ ForeScout CounterACT ไปเรียบร้อยแล้ว คราวนี้เราจะมาดู. New Title Posts Recent Message Time Column; 0 App for QRadar Discussions: 0 Posts 14 App for QRadar Articles. Latest Topic - Palo Alto Networks App for QRadar Troubleshooting Guide. Breaches happen, but how do you respond? With IBM Security QRadar®, you can gain comprehensive insights to quickly detect, investigate and respond to potential threats. Gain actionable insights, quickly identify the top threats and reduce the total alert volume. Patching issues doesn’t offer any long-term guarantee, is usually carried out too late, and just adds more complexity. And that’s where IBM QRadar comes in. Capable of accurately detecting suspicious activities in real-time, QRadar. Configuring an undocumented protocol.59 Chapter 8.
Qradar Ahnlab 7
Healthcare IT (HIT) Security is garnering greater attention among healthcare organizations, though most HIT execs indicate they are not fully prepared. In fact, a recent report by the SANS Institute indicates that healthcare organizations are being compromised at an “alarming” frequency. Given the hefty average cost of an incident coming in at a whopping $800,000, and the fact that over 60% of healthcare organizations reported some type of security breach in 2013, it’s not too surprising that a new urgency is being given to improving security.
This is no small endeavor though. Long gone are the days when putting in place a firewall and an anti-virus solution were sufficient to protect your organization. Today’s CISO has to concern herself with security across many fronts, such as:
- Are our network devices appropriately configured and not using factory default accounts?
- Has anything new been added to the network, or changes made to existing assets that could increase our risk exposure?
- Are we seeing anything suspicious among virtualized server or communication among these systems?
- Are our mobile devices secure?
- Do our servers and laptops have the current security patches and updates to our antivirus solution deployed?
- Is any abnormal traffic occurring on the network, either by volume or abnormal protocols from specific endpoints?
- Are existing web applications under attack?
- Are new web applications under development hardened and safe from common attacks?
- Is communication taking place with known malevolent external sites?
- Are unauthorized accounts, including internal staff, attempting to increase account privileges or making repeated failed login attempts?
- Is PHI being inappropriately accessed or transmitted?
- Does anything in the thousands of log files generated from these systems indicate something is amiss?
It’s a daunting challenge, with a significant penalty in fines, loss of customer trust and organizational reputation at risk should something be missed. In many cases, organizations have implemented point solutions to address some of these individual challenges. However, keeping tabs on all of these individual security solutions and prioritizing where the most significant risk lies can be overwhelming. Similarly doing forensics to identify the root cause of an incident to prevent a recurrence is equally challenging for HIT security personnel whose departments are traditionally underfunded (a recent HIMSS survey showed 49% of respondents spent less than 3% of overall IT budget on security). On top of all of this, security teams must be able to do the reporting required for regulations such as HIPAA, PCI and SOX.
If any of these challenges sound familiar, you should take a look at security intelligence and SIEM solutions like IBM’s QRadar. QRadar has been the leading SIEM solution in Gartner’s magic quadrant for the past 5 years. It provides a customizable role-based dashboard prioritizing security issues that need to be addressed, and providing extensive capabilities to drill down and investigate suspicious activities. It can receive data from numerous endpoints and security solutions, but it also includes a rich set of capabilities for:
- Network traffic monitoring, both physical and virtual flows, including layer 2, 4 and 7 data
- Flow analysis, including correlation and behavioral analytics
- Log file monitoring and analysis
- Risk assessment, including network discovery and risk simulation
- Vulnerability assessment, including device configuration discovery
QRadar addresses many requirements of the HIPAA Security Rule such as:
Qradar Ahnlab Log
- Comprehensive auditing of all transactions moving across a healthcare organization’s network and real-time access to months of activity for rapid response to incidents (§164.312 (b)).
- Continuous tracking of inappropriate internal activity such as insider attacks, stealthy scans and inappropriate attempts to access EPHI servers (§164.308 (a) (1)).
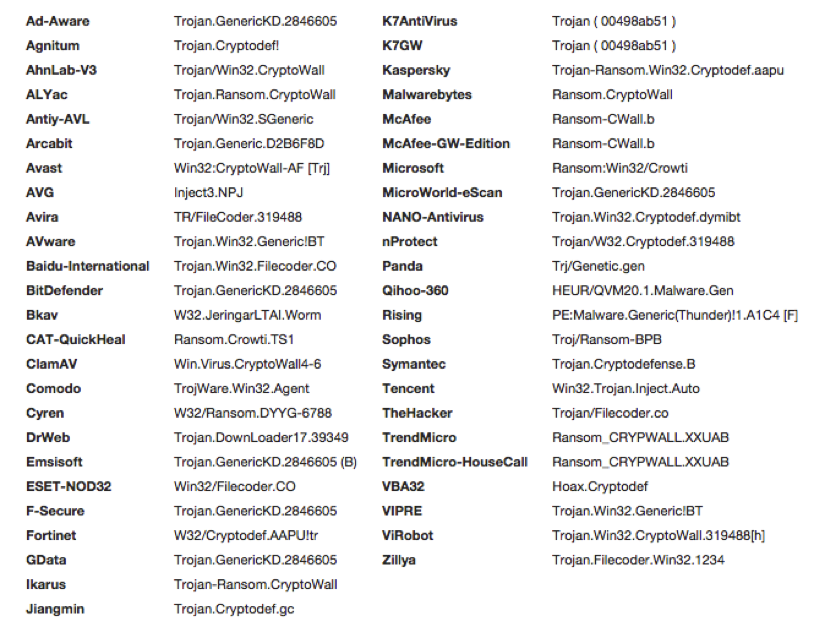
- Detection of new and unidentified threats, such as new worms or Trojans, that pass undetected through signature-based virus checking software and appliances (§164.308 (a) (5)).
- Alerts for violations of internal policies, such as non-compliant usage of a Covered Entities (CE’s) applications (§164.308 (a) (4)).
QRadar includes the following pre-configured report templates to automate the reporting for these and other compliance needs:
- Monthly HIPAA 164.312(a)(1) – 4 / 164.312(d) – 3 User Accounts Additions by Admin
- Daily HIPAA 164.308(a)(6) – 3 Incident Response Summary
- Network Traffic Volume
- Daily Top Targeted IPs by VA Risk
- Weekly Top Attacking Hosts
- Monthly Top Targeted Hosts
- Remote Access Activity Summary
- Daily HIPAA 164.308(a)(4) – 1 / 164.312(e)(1) – 1 Internal Network to Internet Traffic
- Weekly HIPAA 164.308(a)(8) – 3 / 164.308(1)(8) – 5 Vulnerability Report
- Monthly HIPAA 164.312(e)(1) – 2, 3, & 4 Traffic to Trusted Segments
- Daily HIPAA 164.308(a)(4) – 1 / 164.312(c)(1) – 2 Traffic Summaries (Details)
- Monthly Top Attacking Hosts
- Daily Top Targeted IPs
- Weekly Top Targeted Hosts
- Daily Top Targeted Hosts
- Top Users by Remote Access Activity
- Weekly HIPAA 164.308(a)(6) – 3 Incident Response Summary
- Daily Top Attacking Hosts
- Weekly Top Virus Sources and Destinations
- Daily Top Security and Policy Offenses
- Weekly HIPAA 164.308(a)(4) – 1 / 164.312(c)(1) – 2 Traffic Summaries (Details)
- Weekly HIPAA 164.308(a)(4) – 1 / 164.312(c)(1) – 2 Traffic Summaries (Time Series)
- Weekly HIPAA 164.312(e)(1) – 2, 3, & 4 Traffic to Trusted Segments
- Weekly Top IPs for Blocked Spam • Daily HIPAA 164.308(a)(4) – 1 / 164.312(c)(1) – 2 Traffic Summaries (Time Series)
- Monthly Top IPs for Blocked SPAM
- Daily Top Virus Sources and Destinations
- Daily HIPAA 164.312(e)(1) – 2, 3, & 4 Traffic to Trusted Segments from Untrusted Segments
- Daily Top IPs for Blocked Spam
- Network Traffic Volume


Unlike other solutions in this space, QRadar’s virtual or physical appliances are straightforward to deploy, with some implementation projects completed in as little as 3-5 days. CDW’s internal IT team selected QRadar to secure our own environment.

Need to learn more? Post your questions below and reach out to your account manager to arrange a deep dive.